Windows Live Mail Examine, Forensics Solution to Find Evidence of EML File

Before starting with Windows Live Mail forensics & its mail extension EML file forensics and for Windows Live Mail Examine, we need to understand how Windows Live Mail saves emails data in Windows Operating System.
Windows Live Mail, a group app of Windows Essential Suite is a freeware app and it has 290+ million active accounts. It effectively maintains multiple mail accounts, contacts, calendars, & other data. WLM supports POP3 (Post Office Protocol), Internet Message Access Protocol (IMAP) as incoming server & SMTP (Simple Mail Transfer Protocol) for outgoing server.
File Extension & Location of Windows Live Mail Data Files
To know Windows Live Mail Forensic & Examine, firstly we should know where Windows Live Mail data file is actually stored, so, lets’ know about it. Windows XP’s Outlook Express was replaced by Windows Vista Mail in Windows Vista OS, which was further replaced by Windows Live Mail in Windows 7 and later versions as default email client. WLM stores all its data at the location of “C:\ Program Files\ Windows Mail”. Mails data of Windows Live Mail is saved in .eml file format with mailbox tree information.
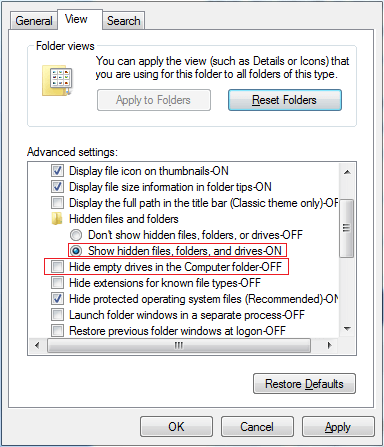
Windows Live Mail has additional information that needs to show mail data. Firstly, you have to apply the given options to view hidden mailbox & file formats:
Control Panel > Folder Options > View > Show hidden files and folders
Control Panel > Folder Options > View > Hide extensions for known file types (uncheck it)
Let’s know the default mails saving location of Windows Live Mail in different OS –
Windows XP: C:\ Users\[ UserName]\ AppData\Local\ Microsoft\ Windows Live Mail
Vista or Windows 7: – C:\Users \[UserName]\ AppData\ Local\ Microsoft\ Windows Live Mail
Windows 8: – C:\Users \[UserName]\ AppData\ Local\ Microsoft \Windows Live Mail
Windows 10: – %UserProfile%\ AppData\ Local \Microsoft\ Windows Live Mail.
From the above explanations, examiners can simply search the location of .eml file in individual OS but they should also know that Widows Live Mail stores contacts data in contact.edb file.
Also read:
Operation Functions of Contact Database
Windows Live Mail has two operation modes for saving contact database –
- Default mode (offline) – No need to sign in with Live ID.
- Live ID mode (online) – Live ID sign in to Windows Live Mail
WLM is operated in single mode function at once. When viewed in Live Mail, contacts are distinctive in each mode.
Windows Live Mail Contact Database
- WLM stores its all contacts in single file that is called contact.edb.
- Every mode of Windows Live Mail should have a single contact.edb file (there may be same name, but saved on different location.)
- Every Live ID maintained in Live ID (online) mode should have distinctive contact.edb file
- The contact file of WLM default mode (offline) is stored in a hidden subfolder called DBStore by default. For reading or viewing the DBStore mailbox, you have to arrange the Windows Explorer to Show hidden files or folders and protected Operating System files.
Default DBStore mailbox location in OS
Windows Live Mail 2011 (Pre QFE3 Edition) – Windows Vista & 7 – C:\Users\ Windows Username\ AppData\ Local\Microsoft\ Windows Live\ Contacts\ Default\ 15.4\ DBStore
Windows Live Mail 2011 (QFE3 Edition) – Win Vista & 7 – C:\Users\Windows Username\ AppData\ Local\ Microsoft\ Windows Live\ Contacts\ Default\15.5 \DBStore
Note: – The default DBStore mailbox is hidden mailbox of 15.5 mailbox.
The default location of DBStore mailbox in Live ID mode of Windows Live Mail 2011 (Pri QFE3 Edition) – Win Vista & 7: – C:\Users\(username)\AppData\Local\Microsoft\Windows Live\Contacts\(Live ID)\15.4\DBStore
C:\Users\(username)\AppData\Local\Microsoft\Windows Live\Contacts\(Live ID)\15.5\DBStore
Forensically save Deleted or Corrupted EML Files
In these days, quick messengers, social networking sites & mails are the major source and carriers of information. These are mostly used by commercials for professional communication. Therefore, if some information is deleted accidentally or otherwise, it may cause problem to users. To stabilize such catastrophic conditions, WLM has deleted items mailbox. The mailbox saves all deleted items that users delete from any mail folder. Though in some cases, users use hard deletion, which is not easily handled by them. But deleting / erasing mail message permanently doesn’t mean that can never get them back, it can be recovered forensically.
Forensic outlining of mails is utilized for retrieving data from EML files for performing analysis. While doing so, we should be aware of the mail format and functionalities related to them. In Windows Live Mail case, the file format of mail is .eml & more information can analysed with forensic techniques.
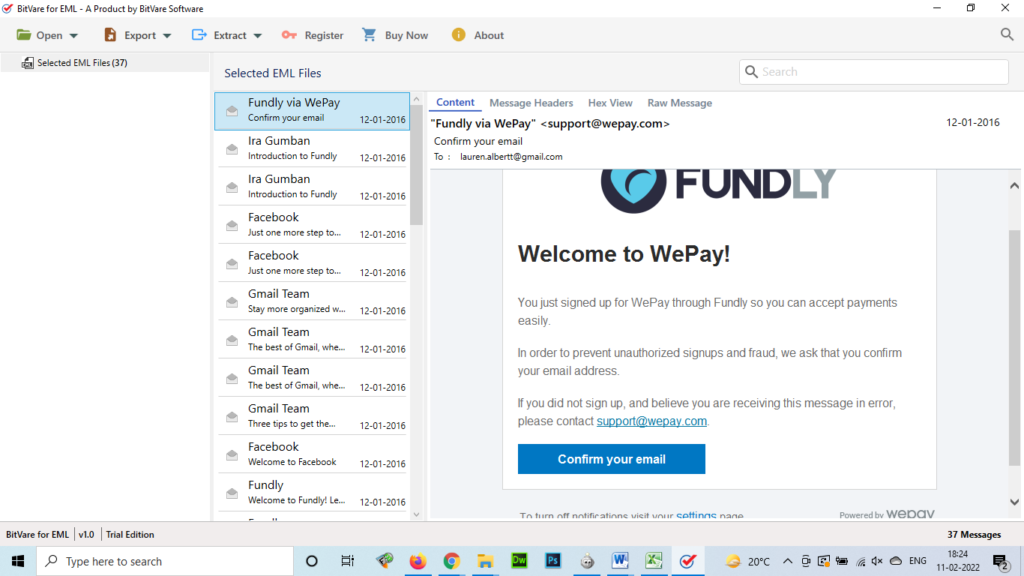
Examine EML files (Mail format of WLM) with BitVare Software
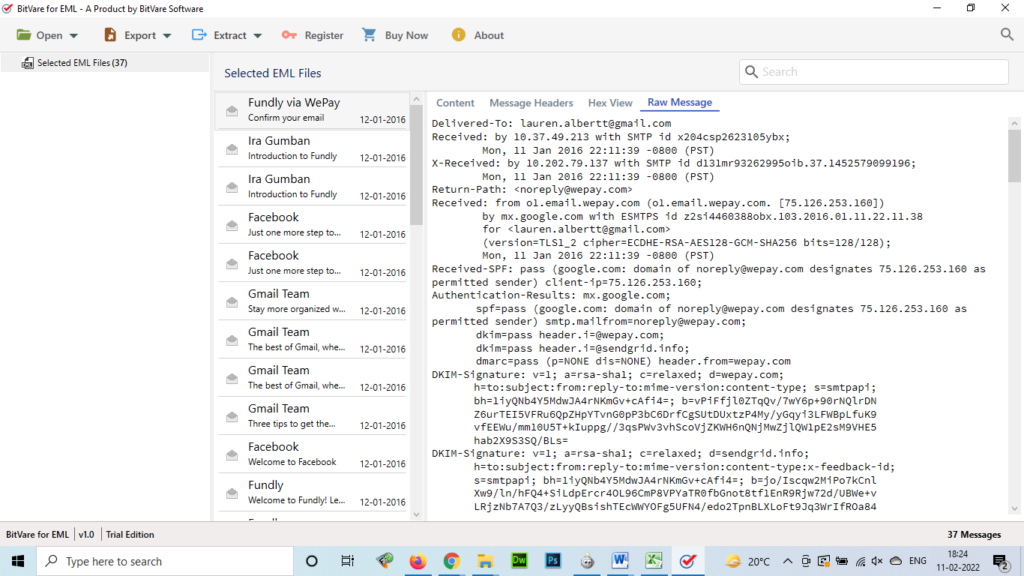
Forensic mail examines solutions have the competence to analyse & examine EML files with its multiple properties – Complete Content View for general mail body analysis, Hex view for hexadecimal code. Message header option helps to examine mail properties, Raw messages, etc. These multiple functions of the BitVare for EML software helps in Windows Live Mail forensic analysing of uploaded data files.
Content View
Generally, Content view option is helpful for everyone to view mail properly. It displays mail with complete view without any change. So easily read & view your Windows Live Mail EML mail.
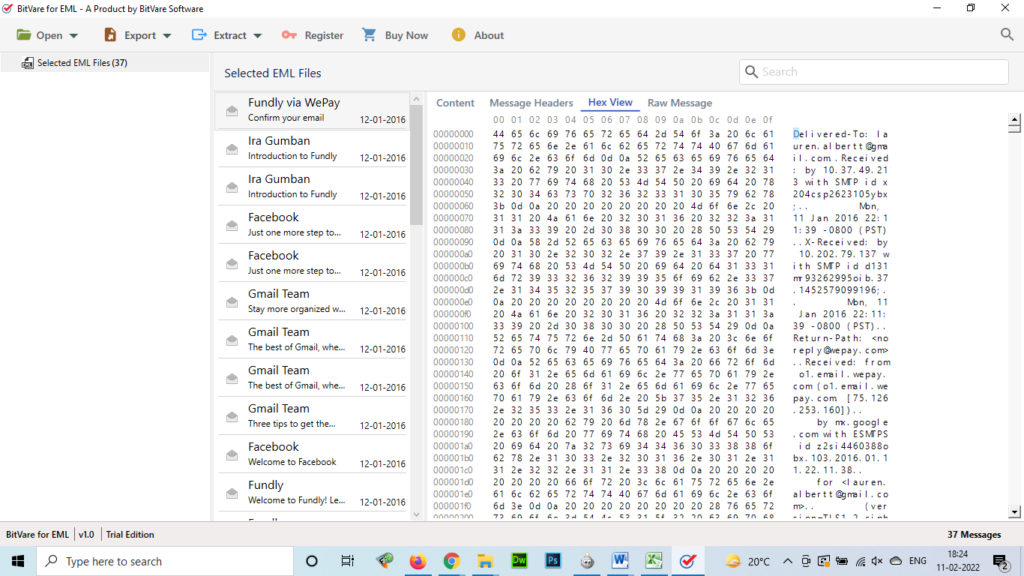
Hex View
Hex View (Hexadecimal code examination) simplifies the complete structure of binary codes. These values can make the investigation process simpler to assist & understand for the judgement of crimes such as mail crimes.
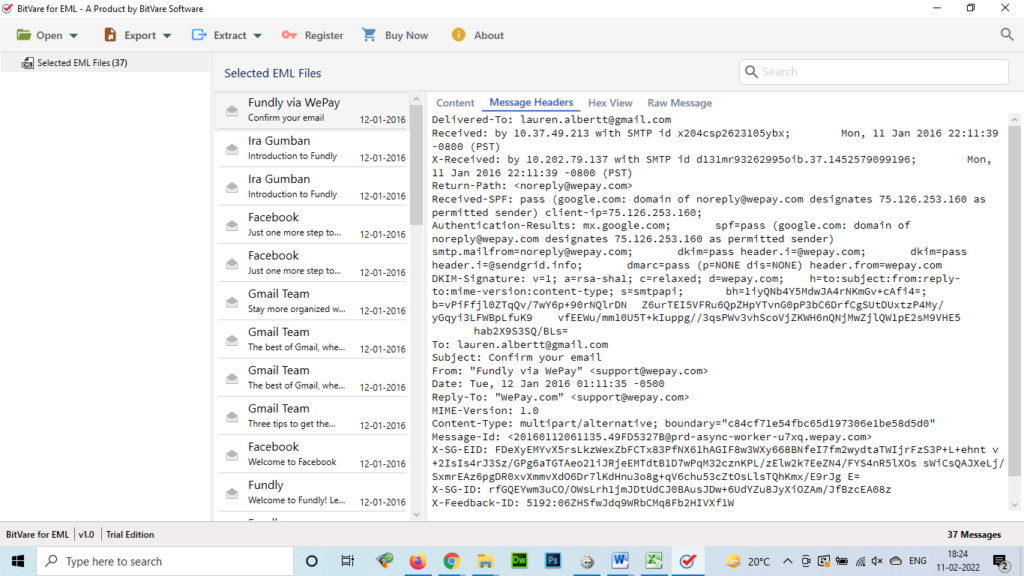
Message Header
Message header is also a useful option to examine the provided information for tracking mails. It assists to search original sender’s MIME edition, IP Address, Content Type, X-Priority, Message-IDs, etc.
Raw Messages
The Raw view option helps investigators to access content examine by analysing internet script or HTML code of the mail data.
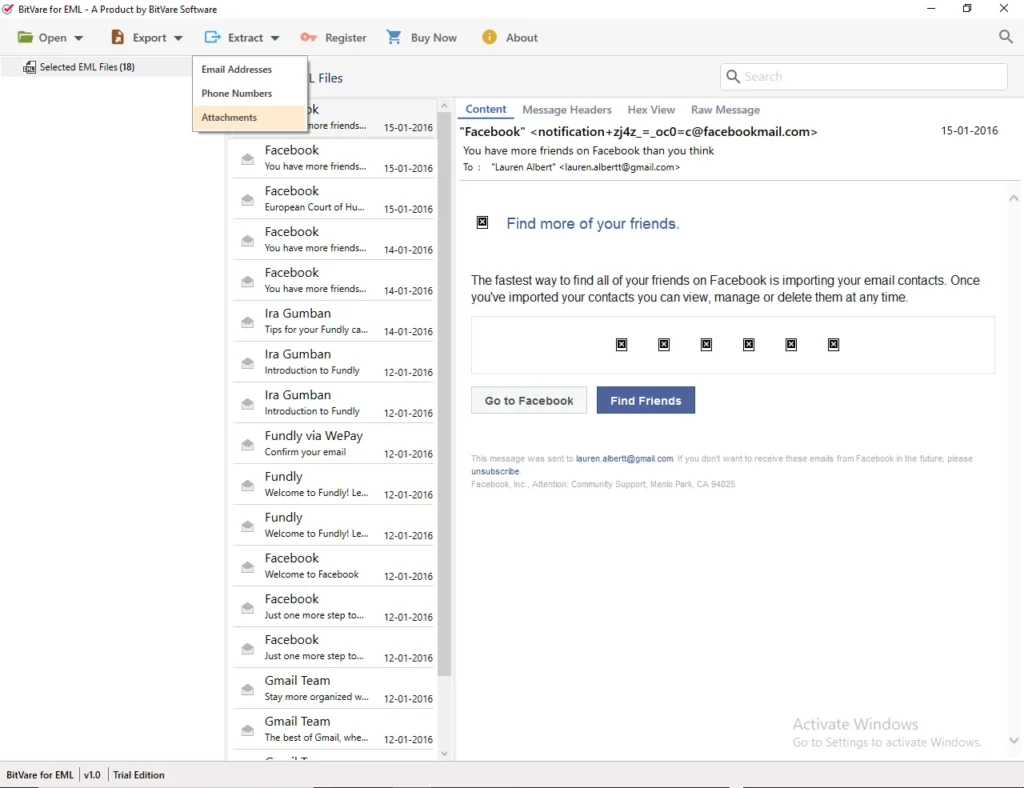
Extract Attachments, mail address & phone numbers for analysing
Attachments are the very important for digital forensics and the user-friendly software understands all needs of investigations. So it has extract option in which, investigators can extract attachments, phone numbers & mail address of emails to deeply examine EML file.
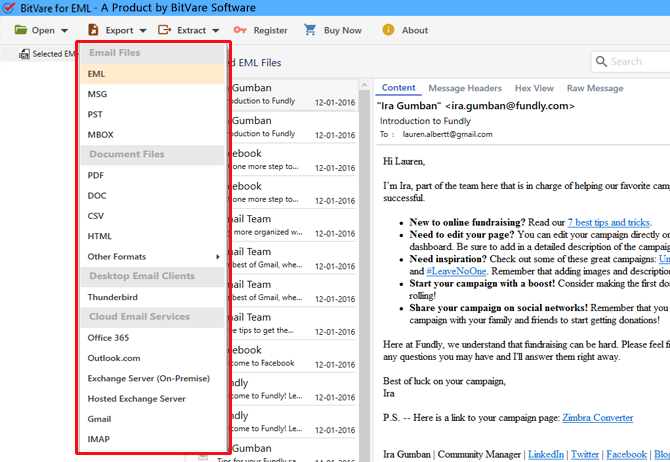
Export & Maintain Evidence
A forensic analyst must always keep the steps or stages of examinations involved to search the relevant proofs to crime scene. It assists investigators to display the investigation process related to the case more accurately in front of legal authorities. After finding the evidence within EML files, the last step of mail examining process is reporting. It can execute by saving the case data & evidence saved from the EML files into legal file format – PDF, MSG, etc, which is beneficial for judicial proceeding.
Conclusion
In this blog, we explained Windows Live Mail, its mail extension, contacts & its locations. Here, we also recommend a mail forensic software that helps investigate EML files in different views for good examine. The main goal of BitVare Software is to fetch out efficient evidence; It may enable the offenders to successfully prosecute. The solution is the accurate, fast & simple to handle for mail forensics investigations.